Xu Zewei, 33, was taken into custody in Milan as he arrived from China, marking a significant development in a case that has drawn international attention.
HOUSTON — A Chinese national accused of orchestrating a sweeping cyber espionage campaign that targeted U.S. COVID-19 research and confidential information about American policymakers has been arrested in Italy at the request of the United States.
Authorities say Xu Zewei, 33, was taken into custody in Milan as he arrived from China, marking a significant development in a case that has drawn international attention for its scope and alleged state sponsorship. Xu and a second suspect, Zhang Yu, 44, are charged in a nine-count indictment with computer intrusions that spanned from February 2020 to June 2021 and allegedly compromised thousands of computers worldwide.
Hackers targeted pandemic research
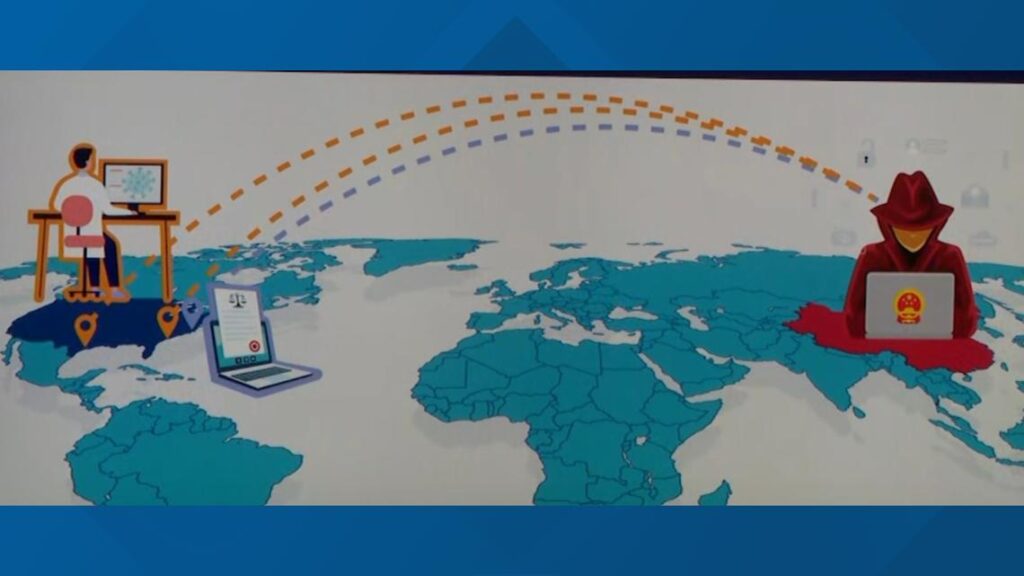
According to federal prosecutors, Xu and his co-conspirators, acting under the direction of China’s Ministry of State Security (MSS) and its Shanghai State Security Bureau, targeted leading U.S. universities, immunologists and virologists. The indictment alleges the hackers stole sensitive COVID-19 research, including data critical to vaccine development, as the world grappled with the pandemic.
Authorities said Xu, employed by Shanghai Powerock Network Co. Ltd., worked as part of a network of Chinese companies contracted to conduct government-sponsored hacking. The group’s activities included breaking into university networks and accessing the email accounts of researchers involved in COVID-19 studies.
The HAFNIUM campaign
Beginning in late 2020, Xu and others allegedly exploited vulnerabilities in Microsoft Exchange Server, launching the “HAFNIUM” cyberattack that federal officials described as “indiscriminate” and “reckless.” The campaign compromised thousands of computers, including those belonging to a Texas university and a global law firm with offices in Washington, D.C.
The hackers are accused of searching for information about U.S. policymakers and government agencies, using search terms such as “Chinese sources,” “MSS,” and “HongKong.”
U.S. response and legal ramifications
U.S. officials emphasized their commitment to tracking down foreign hackers, regardless of how long it takes.
“Even if it takes years, we will track hackers down and make them answer for their crimes. The United States does not forget,” said Nicholas Ganjei, U.S. Attorney for the Southern District of Texas.
Xu faces charges that include wire fraud, unauthorized access to protected computers, intentional damage to protected computers, and aggravated identity theft. If convicted, he could face decades in prison and fines up to $250,000 per conviction. Zhang remains at large, and the FBI is seeking information on his whereabouts.
Broader implications
The case highlights what U.S. officials describe as a broader Chinese government strategy of using private companies and contractors to obscure its involvement in cyber espionage. This approach, authorities warn, increases the risk of widespread victimization and leaves more systems vulnerable to future attacks.
In April 2021, the Justice Department announced a court-authorized operation to remediate hundreds of computers in the U.S. left exposed by the HAFNIUM campaign.
Ongoing investigation
The FBI’s Houston Field Office is leading the investigation, with federal prosecutors from the Southern District of Texas and the Justice Department’s National Security Division handling the case. The public is urged to contact the FBI with any information regarding Zhang Yu’s whereabouts.